ולידציה -Computerized System Validation
This article was written by Iian Shaya, validation,automation and control expert
Each system has a specific life length dependent on the time taken for the system to become outdated; this life length is called System Life Cycle – SLC
The SLC is defined as an organized method to plan develop, test, modify and maintain a computer-based system
:The SLC requires the following
Unit tests – The test protocols shall be traced to low level design document and will be approved by the user prior to execution. The approval of the report shall be performed by representatives of the user’s validation team, IT QA
Management
Requirements
Design
Implementation coding
Integration
Installation
Operation and support
Maintenance
Change control
Management
Management must identify and provide an appropriate validation environment. Refer to Code of Federal Regulations (CFR) 820.20 which is a law issued by the US
:A plan must be developed to include
Validation tasks for each life cycle system
Methods and procedures for each validation task
Criteria for initiation and completion of each validation task
Inputs for each validation task
Outputs for each validation task
Criteria for defining and documenting outputs in terms
Requirements
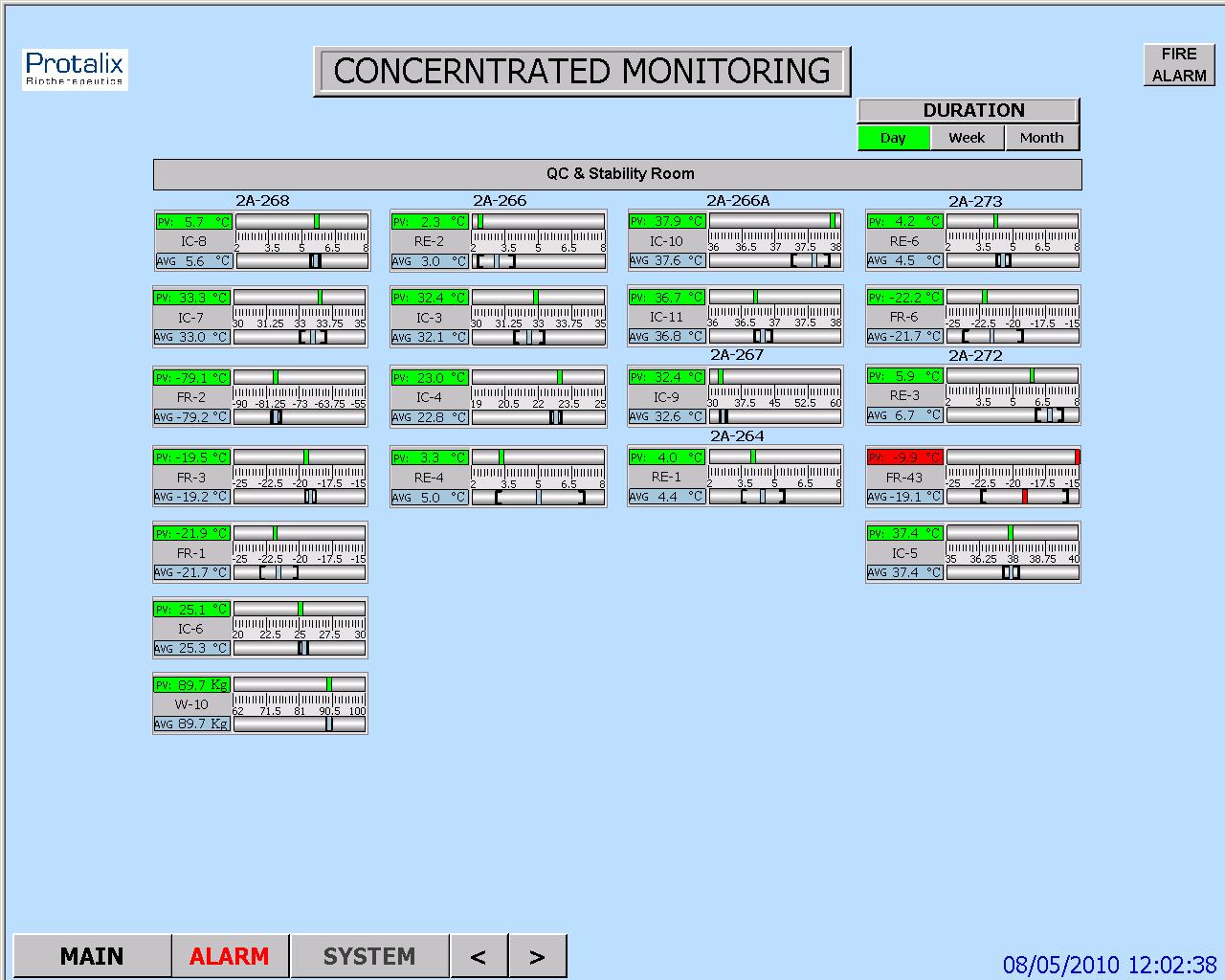
:Electronic Records
The system/product should ensure cover of the following requirements, related to Electronic Records
The system/product must generate accurate and complete copies of records in both human and electronic form
The system/product must protect records to enable their accurate and ready retrieval throughout the records retention period
The operational system/product checks must enforce the proper sequencing of steps in a process, as appropriate
:The system/product must ensure that only authorized individuals can
Criteria for defining and documenting outputs in terms
Use the system, logical access
Electronically sign a record
Access the operation or computer system input, including time/date and idle session
Access the operation or computer system output device
Alter a record
Audit Trail
The system must cover the following requirements related to Audit Trail
The audit trail must be secure
The audit trail must be computer generated
The audit trail must include time and date stamp
:The audit trail must independently record the date/time of operator entries and actions that
Create electronic records
Modify electronic records
Delete electronic records
The system/product must ensure that changes to electronic records cannot obscure previously recorded information
The audit trail records must be maintained for at least as long as the retention of the underlying records
The audit trail records must be available for review and copying
Electronic Signatures – ES
The system will relate to ES (linkage between the record and the signature) during the working process under the following requirements
The ES must contain the printed name of the signer
The ES must contain the date and time of signing
The ES must contain the meaning of the signing, such as approval, review, responsibility etc
The ES must include a part of any human readable form of the electronic record, such as electronic display and/or printout or report
The 3 items above must have the same controls as for electronic records
The signatures linked to their respective electronic records must ensure that these records cannot be cut, copied, or otherwise transferred by ordinary means for the purpose of falsification
The system must ensure that the electronic signature is unique to one individual and not be reused by, or reassigned to, anyone else
The electronic signature must employ, at least 2 identification components, such as identification code and password
The system must enable customization of workflow signing rules (using one or all signature components in different scenarios), when an individual executes a series of signings during a single or continuous period of controlled system access
The system must be contained into a unique Digital Signature (biometrics, token, cards, cryptographic symbols etc
Controls for Identification Codes/Password
The combination of the identification code and password must be unique
The combination of the identification code and password must be revised, e.g., to cover such events as password aging
Unauthorized use of password identifications and devices must be reported to the system security unit and/or management, as appropriate
This article was written by Iian Shaya, validation,automation and control expert